Remote Control
Hidden Effects of Connected Devices
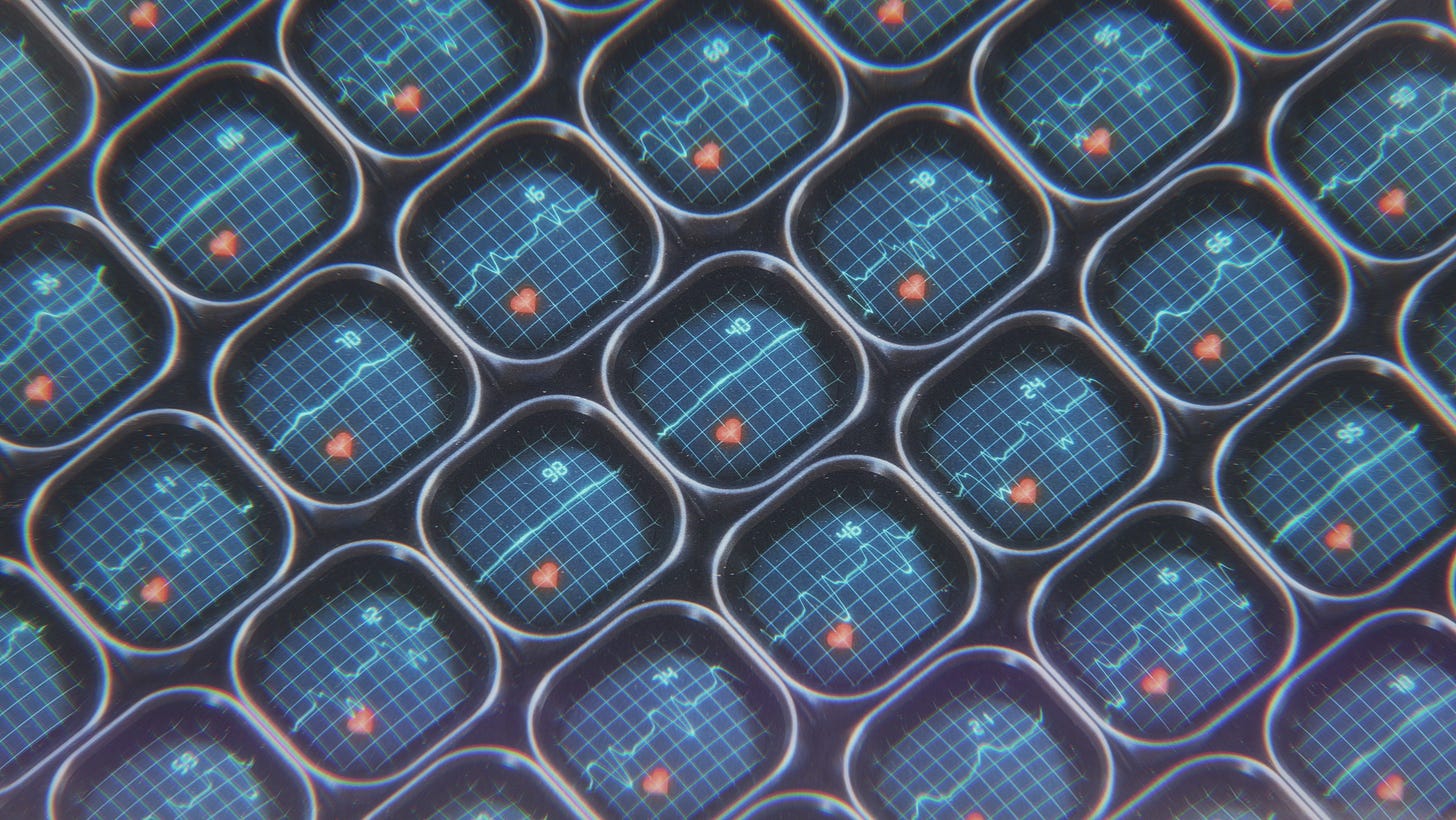
Imagine a future where pharmacies are embedded within our bodies. Life-saving and mood-regulating chemicals are delivered on demand—as long as your insurance subscription remains active. Researchers have already developed an implantable device that can monitor vital signs and pump out naloxone in case of an overdose. But what if such life-assisting technologies began to be conditionally revoked, affected by outages, or even hacked?
Physical purchases once meant ownership. But connected devices are making their use conditional. Most of the disruptions we encounter might only cause minor inconveniences, like an ink cartridge being remotely disabled for a missed subscription payment. Yet as connected devices proliferate, they’re entering more consequential and unexpected arenas like paywalls that limit how much your car’s wheels can turn.
When you buy connected hardware, you’re often not only buying a product controlled by corporate terms, but also entering a network of dependencies that can turn against you in ways you might not anticipate or be able to fix. For instance, smart beds designed to capture biometric data and adapt to each user got stuck in reclined positions and blasted heat during an Amazon Web Services (AWS) outage, with no way to adjust their settings. These failures are also scaling beyond personal devices: self-driving Waymos became immobile during a blackout in San Francisco, blocking vehicles and getting stuck in busy intersections.
Connected hardware also creates novel opportunities for abuse. Those with system access have gone as far as weaponizing smart homes to trap and torture partners: locking them inside and manipulating temperatures. But exploitation can come from outsiders as well: hackers have turned connected children’s toys and smart home robots into surveillance devices, and in South Korea, over 120,000 cameras were compromised in homes and businesses, including a gynecologist’s clinic, to produce sexually exploitative content.
These were the plots of ‘80s sci-fi thrillers exploring far-off futures, but are now a creeping reality. This makes it crucial to ask deeper questions that inform what we design, use, and buy into. Here are three to consider:
What hidden doors lie within?
“We have a tremendous amount of hardware makers that are just pushing out hardware and letting somebody else design the software. They tend to have very poorly written software powering the devices,” security researcher Brian Krebs told VICE Blueprint. What doors are opened when foundational aspects of a product are outsourced or overlooked?
Security researchers have been able to use Shodan, an IoT search engine, to readily find devices that are streaming directly to the internet. And each connected device on a network can expand the attack surface. One casino’s high-roller database was stolen through a lobby fish tank thermometer. Flaws in a car dealership portal exposed customer data and could have allowed hackers to remotely control some vehicle features from anywhere. A hobbyist who used Claude Code to create an app to control his robotic vacuum with a video game controller, unwittingly gained access to 7,000 vacuums across 24 countries, including live camera and microphone feeds.
Hidden doors aren’t only technical either. They can also exist in the gap between purported use and actual implications—like a helpful tool for finding puppies, obscuring mass-surveillance infrastructure.
What survives network and life disruptions?
What form and function does your product take when infrastructure fails or connectivity becomes overwhelming? Does it become completely useless when offline? And when online, do its outputs create an always-on barrage of notifications impacting the senses? Or are there modes in between?
The reality of connectivity risks has inspired new directions towards more local network, cloud-optional approaches like Z-Wave and Zigbee protocols. These enable smart home systems—lights, sensors, security—all to function without the internet on local mesh networks. Additional benefits include reduced latency and long-term reliability. One user stated “The best part about my Z-Wave setup is every manufacturer can go out of business and I won’t even notice.”
More analog and singular-purpose devices also offer relief from the daily inundation of notifications and feed fatigue. While local protocols can help with technical reliability, some users are opting out of connectivity altogether. Younger generations are seeking simpler devices over those teeming with features, with searches surging for MP3 players, portable CD players, and even flip phones.
What remains in the afterlife?
Humane’s $700 AI pin became e-waste in less than a year after its debut when its ambitions didn’t meet demand. They reportedly avoided due diligence, ignored the device’s criticisms, and pulled the plug completely, shutting down its servers and deleting user data.
Afterlife problems aren’t only limited to cloud-dependent devices and can extend to higher-stakes situations. They also emerge from support policy decisions, even when companies remain operational. A paralyzed man with a $100,000 exoskeleton encountered a wiring issue with his watch (needed to control the system) and thought it would be a simple fix. Instead, the company told him they don’t support systems over 5 years old, leaving him unable to walk. Patients with Second Sight’s retinal implants faced abandonment when the company pivoted. One user described it as “fantastic technology and a lousy company“ after being unable to get medical information about his implant needed for an MRI—leaving him unable to rule out a brain tumor.
Many of the examples here highlight worst-case scenarios, yet these same technologies are helping people walk, see, and live more independently. The always-on AI functionality of Ray-Ban Meta’s smart glasses stirs privacy concerns, but also provides impactful and affordable accessibility to blind and low-vision users.
Some advanced features may require cloud processing to work in real-time. But where do we draw the line between features that warrant connectivity and core functionality that shouldn’t? And what are the implications of that stance for users, brand reputation, and long-term trust? Eight Sleep, after the AWS outage, promised an offline mode. But can we anticipate such issues before they become headlines?
As designers and users, critical questions around these emerging risk vectors are necessary. Lest we invite a future of remotely brickable body parts.


The examples of the smart beds getting stuck in reclined positions blasting heat and Waymo immobilization were especially powerful. Layered graceful degradation needs to be non-negotiable for connected products that control your physical environment.